Why Crypto Scams Are Not Just a Tech Issue — They're a Messaging Problem
Why the Biggest Crypto Threats Now Exploit Trust, Perception, and User Behavior

Cryptocurrency thefts have shattered previous records in 2025, with over $2.17 billion stolen by mid-year alone. But the most alarming shift is not just the scale of exchange hacks—it’s how criminals are increasingly targeting individual users in more direct and sophisticated ways.
Key Takeaways
- Over $2.17 billion was stolen in the first half of 2025, surpassing the $2.2 billion stolen throughout all of 2024
- North Korean state-sponsored hackers were responsible for the largest single theft - $1.5 billion from ByBit exchange
- Individual crypto wallet attacks now account for 23.35% of all stolen funds through July 2025, making personal security measures critical
- AI deepfake scams are becoming increasingly sophisticated, targeting crypto users with fake celebrity endorsements like Elon Musk impersonations
- Basic security practices still prevent most attacks
- Five proven security measures can protect most crypto investors from common attack vectors
- Crypto content syndication proves effective crypto-marketing can help rebuild reputations and brand trust and loyalty - beginning with absolute transparency on what happened and how it is being corrected
Over $2.17 Billion Stolen: A Rapid Escalation
Cryptocurrency security breaches reached unprecedented levels in 2025, with losses surpassing $2.17 billion by mid-year. This figure nearly exceeds the total stolen across all of 2024, signaling a sharp escalation in both scale and frequency.
The pace of attacks continues to increase, with multiple million-dollar breaches occurring in short timeframes. These trends reflect a shift in both tactics and targets, forcing the industry to rethink how risk is managed.
The ByBit Breach Shows the Scale of Modern Attacks
The February 2025 breach of ByBit stands as the largest single crypto theft to date, with approximately $1.5 billion in Ethereum stolen. Investigations linked the attack to state-sponsored actors using highly coordinated strategies.
Attack Methods
Rather than exploiting code alone, attackers relied heavily on social engineering. By targeting internal systems and gaining access through compromised credentials, they bypassed traditional defenses.
Laundering at Scale
Following the breach, funds were distributed across dozens of wallets and converted rapidly, making recovery extremely difficult. The operation demonstrated not just technical capability, but strategic planning and patience.
AI-Driven Scams Are Changing the Game
Artificial intelligence is accelerating the effectiveness of crypto scams.
Deepfake technology allows criminals to impersonate trusted figures with convincing accuracy. Fake endorsements, livestreams, and social campaigns create a false sense of legitimacy that can persuade users to act quickly.
Beyond impersonation, AI-driven conversations are now used to build trust over time. Victims may engage with what appears to be a knowledgeable contact, only to discover too late that the interaction was entirely automated.
Individual Users Are Now the Primary Target
Cybercriminals are shifting focus.
As institutional security improves, attackers are targeting individuals who often lack strong protection measures. Personal wallets now account for a growing share of stolen funds.
Common attack methods include:
- phishing campaigns
- malicious apps
- compromised websites
- social engineering tactics
More concerning is the rise of physical coercion attacks, where individuals are forced to surrender access to their assets. These incidents are expected to increase as crypto values rise.
Security Still Matters—But It’s Not the Full Picture
Basic security practices remain essential:
- hardware wallets for offline storage
- two-factor authentication
- multi-signature wallets
- asset distribution across multiple wallets
- regular security reviews
These measures significantly reduce risk.
But they do not address how most attacks actually succeed.
Why Crypto Scams Are a Messaging Problem
Most successful attacks do not begin with code.
They begin with belief.
Users are persuaded before systems are compromised. Trust is established before access is gained. By the time a technical action occurs, the decision has already been influenced.
These are not just security failures.
They are messaging failures.
Because in crypto, perception is shaped before protection is tested.
When a Breach Happens, the Damage Isn’t Just Technical
The impact of a breach extends far beyond stolen funds.
It affects:
- user confidence
- community perception
- long-term credibility
In crypto, trust moves quickly—and it disappears even faster.
If communication is delayed or unclear, speculation fills the gap. Once that narrative forms, it becomes difficult to reverse.
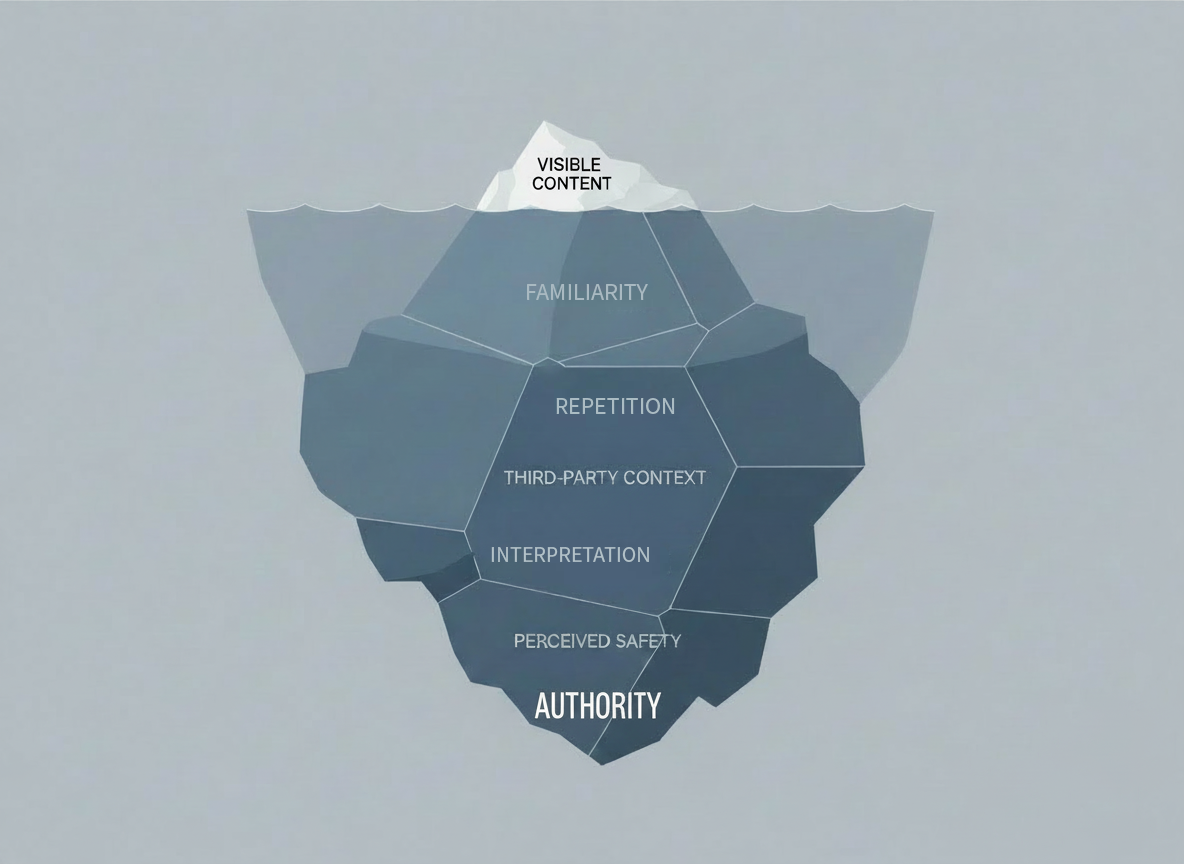
Why Messaging and Visibility Matter After a Breach
How a project responds matters as much as the breach itself.
Clear, immediate communication helps stabilize perception. It signals accountability and control.
But speed alone is not enough.
That message must be seen across the platforms where users are already paying attention. If accurate information is not visible, misinformation becomes the dominant narrative.
This is where search visibility directly shapes how events are understood.
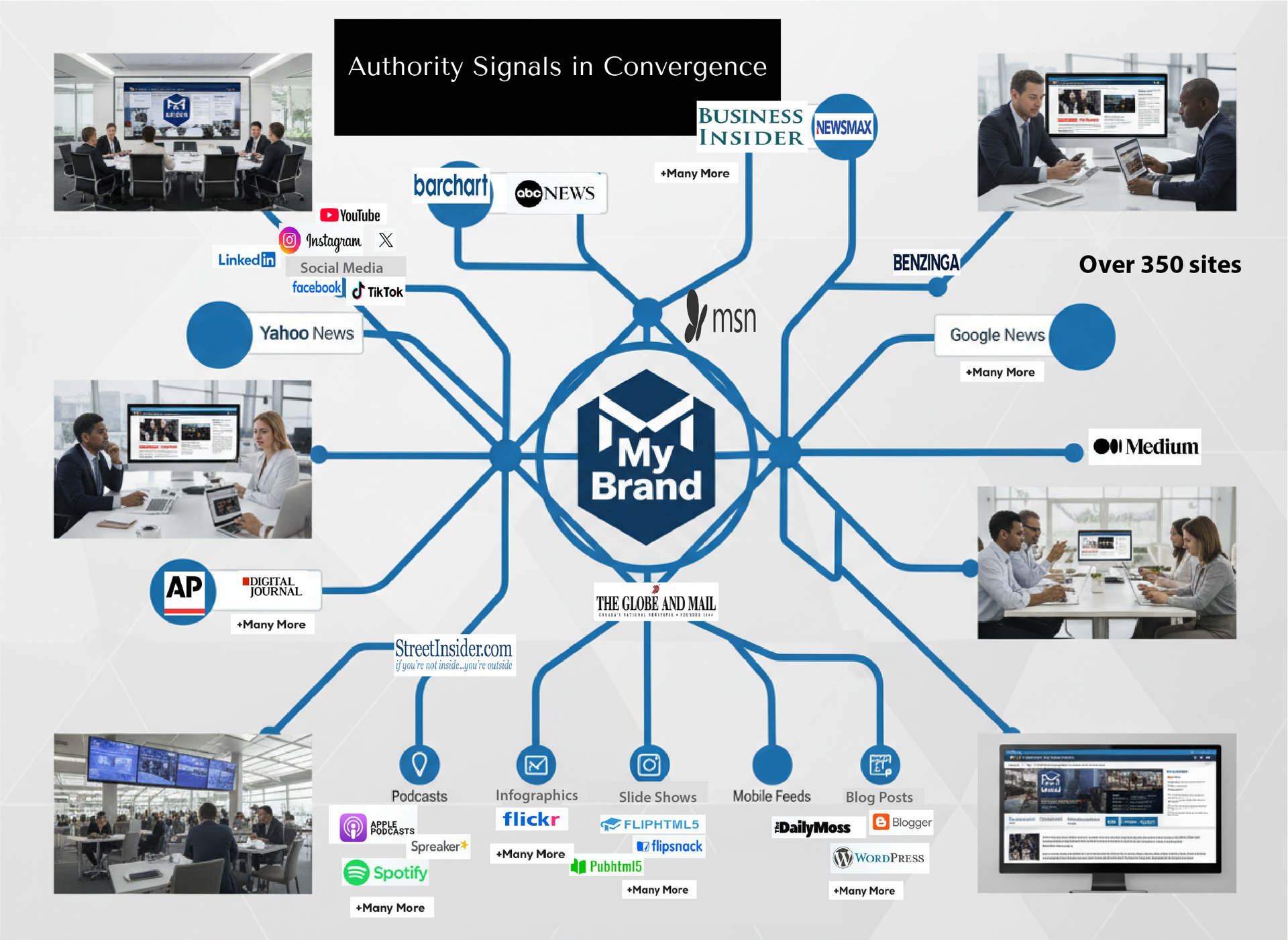
The Role of Content Syndication in Trust Recovery
After a security incident, communication must extend beyond a single announcement.
Information needs to be distributed across:
- crypto-native publications
- trusted media platforms
- high-visibility digital channels
This creates consistency, reinforces transparency, and helps restore confidence across different audiences.
JCH Digital focuses on rapid content syndication to ensure accurate information is distributed quickly and broadly, helping projects stabilize perception and rebuild trust following a breach.
Stronger Security Alone Won’t Solve the Problem
The crypto landscape is evolving.
Attack methods are becoming more advanced. Targets are becoming more personal. And the gap between perception and reality continues to widen.
Security measures are essential.
But they are only part of the solution.
Long-term resilience depends on how trust is built, communicated, and reinforced.
Crypto scams are not just a technology problem.
They are a messaging problem.
And trust is often decided before comparison begins.
Ready to see where your authority stands?
Your name can be visible and still fail to create trust before comparison begins.
If you want to understand how your current authority signals are working, start here.
Request an Authority Compatibility Audit below