Crypto Scams and the New First Responders
Crypto content marketing and syndication is invaluable for affected crypto projects

Crypto security threats are shifting in 2025. Instead of targeting large exchanges, attackers are increasingly going after individual user wallets. This change puts personal asset protection at the center of risk for every investor in the digital asset space. As these attacks become more targeted and more frequent, the response window after a breach is shrinking. In that environment, how a project communicates in the first hours matters as much as the breach itself.
More information is available at https://www.jchdigital.ca/crypto-projects-marketing.
The seriousness of this trend is reflected in significant financial losses. In the first half of 2025, crimes related to crypto assets led to the theft of over $2.17 billion. This amount demonstrates a pressing need for improved defensive measures across the ecosystem.
These losses are driven by attackers using more advanced and deceptive methods. Attack vectors have evolved to include the widespread use of artificial intelligence for creating convincing phishing scams. A report from Hacken noted a 1,025% rise in AI-related crypto hacks compared to the second half of 2024. These tools are used to craft deceptive emails and messages designed to steal private keys.
What Happens in the First 24 Hours After a Crypto Breach
The first 24 hours after a breach are chaotic.
Users are confused. Information is incomplete. Speculation spreads faster than facts.
In most cases, the project itself is silent while internal teams assess the damage. That silence creates a vacuum, and that vacuum gets filled by third-party voices, forums, and social media threads.
By the time an official statement is released, the narrative is already forming without them.
Why Trust Collapses Faster Than the Hack Itself
The technical issue is only part of the problem.
The larger issue is perception.
Investors are not evaluating code. They are evaluating risk.
When information is inconsistent or delayed, confidence drops immediately. Withdrawals increase. Sentiment shifts.
At that point, recovery is no longer about fixing the breach. It is about stabilizing belief.
The Real Role of Visibility in Crisis Response
Most projects treat communication as an update.
In reality, it is a control mechanism.
The speed and reach of information determine whether a project looks transparent or unprepared.
If accurate information is not widely visible, misinformation becomes the dominant narrative.
This is where visibility stops being marketing and starts acting as infrastructure.
A passive approach to security is no longer enough. Stronger, proactive measures are now required to protect digital assets. Long-term holdings are better secured in offline cold storage wallets, keeping them out of reach from online threats. Two-factor authentication should be enabled across all exchange accounts and related services to add an extra layer of protection. Strong, unique passwords for every platform are no longer optional. They are a basic requirement in an environment where attackers are actively exploiting weak points.
Why Most Crypto Projects Fail to Recover
Recovery failure is rarely due to the breach alone.
It comes down to delayed communication, limited reach, and fragmented messaging.
Projects rely too heavily on their own channels, assuming their audience will find the update.
They don’t.
Instead, the conversation continues elsewhere, without context, and often without correction.
Why Content Syndication Acts as a First Response System
After a breach, speed is not optional.
Information needs to move faster than speculation.
This is where content syndication changes the outcome.
Instead of relying on a single announcement, the message is distributed across multiple independent platforms, reaching audiences where they are already consuming information.
This includes crypto-native media, general news platforms, and social channels where discussions are actively forming.
The goal is not promotion. It is narrative control.
When accurate information appears consistently across trusted environments, it stabilizes perception and reduces uncertainty.
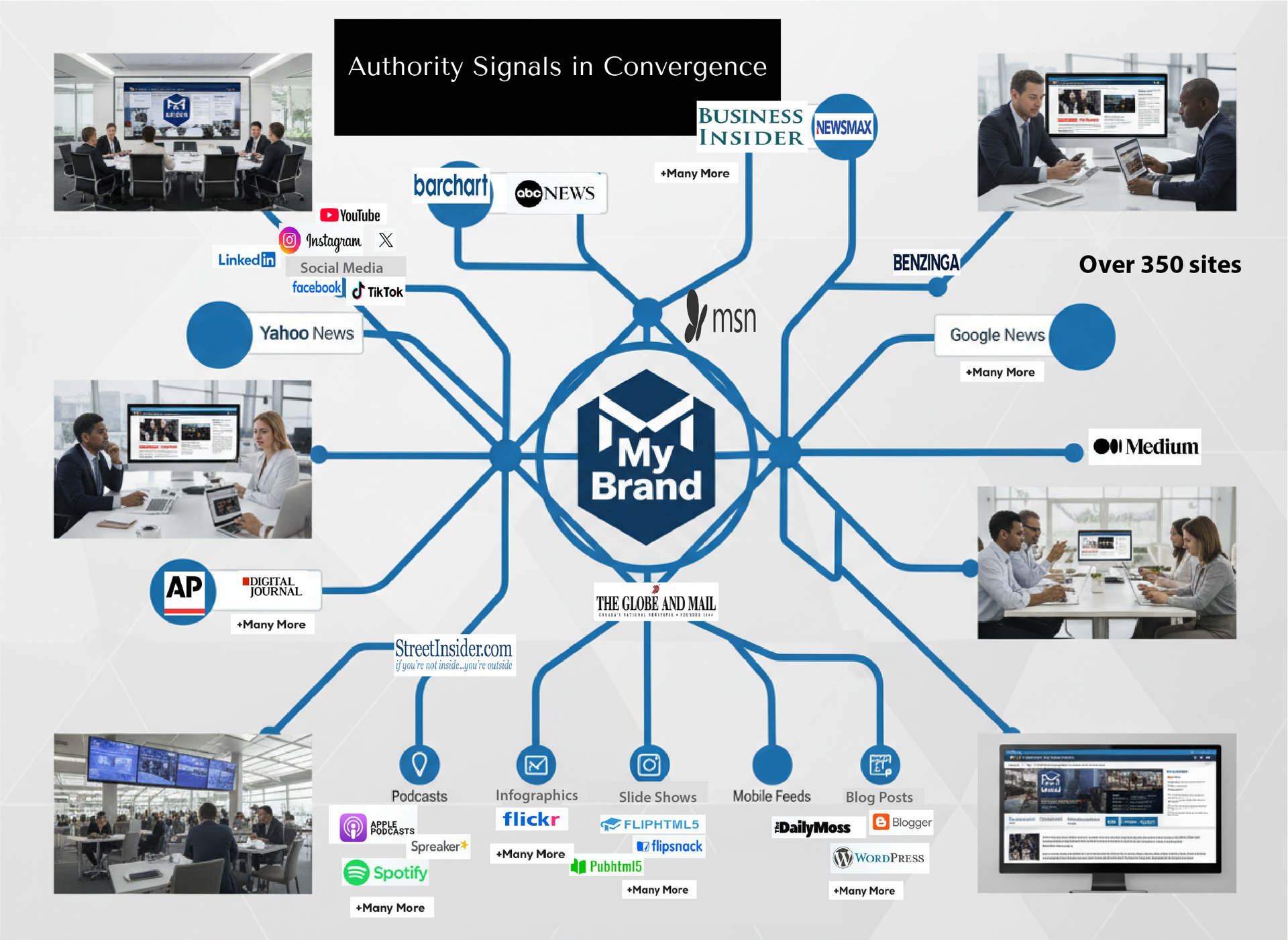
That is why crypto content marketers are the new first responders for security breaches. Companies such as JCH Digital specialize in crypto marketing and making sure information is immediately and broadly disseminated not only on over 70 Google News Approved crypto news sites. But also in over 300 high authority high trust sites beyond the crypto investor world and in formats the buyers use (social media, video shorts, X etc).
Instant content syndication is key. Within 24 hours the news is across the internet in multiple formats ensuring transparency for the investor and the consumer, helping to rebuild trust and loyalty.
JCH Digital specializes in rapid content syndication for crypto projects during high-risk events. When a breach occurs, information needs to move quickly and consistently across multiple trusted environments. That includes distribution across Google News-approved crypto publications, broader authority sites, and the platforms where discussions are actively forming. The objective is not visibility for its own sake. It is to stabilize perception, reinforce transparency, and help projects regain trust before uncertainty defines the narrative.
Learn more about JCH Digital at https://www.jchdigital.ca/.
How confident are you about your messaging if a data security breach happened at your firm?
Ready to see where your authority stands?
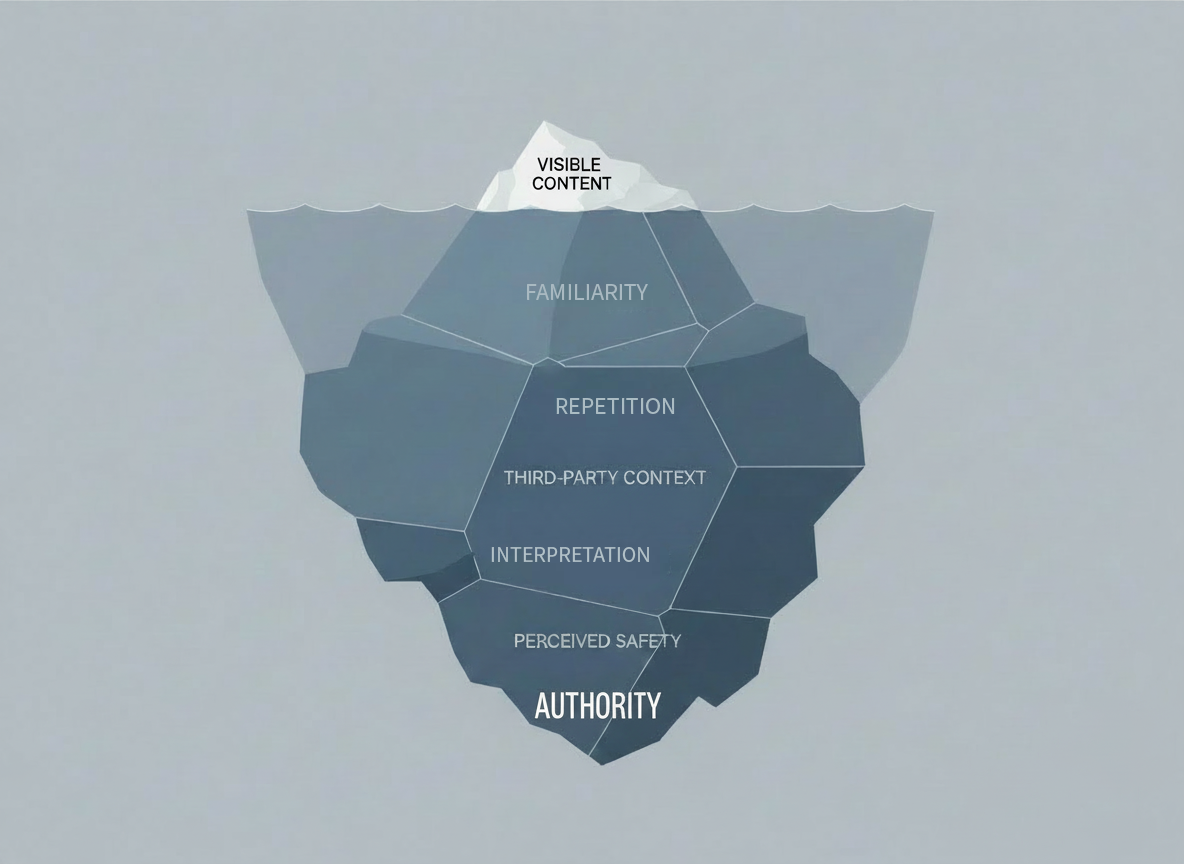
Your name can be visible and still fail to create trust before comparison begins.
If you want to understand how your current authority signals are working, start here.
Request an Authority Compatibility Audit below